In here we prefer success stories over anything else. Like, “one telecom operator was in an urgent need to re-engineer its traffic due to an explosive usage growth” – which, in turn, was leading to even bigger ARPU. Steps were made to prioritize different kinds of traffic, thus offering the customers more personalized tariffs with more advanced billing, better handling of “heavy” content, and in general providing more satisfying customer experience to end users. To quite an extent goals were achieved by implementing Deep Packet Inspection method.
It’s the true story, by the way, so no troll face is to follow.
Data Transfer 101
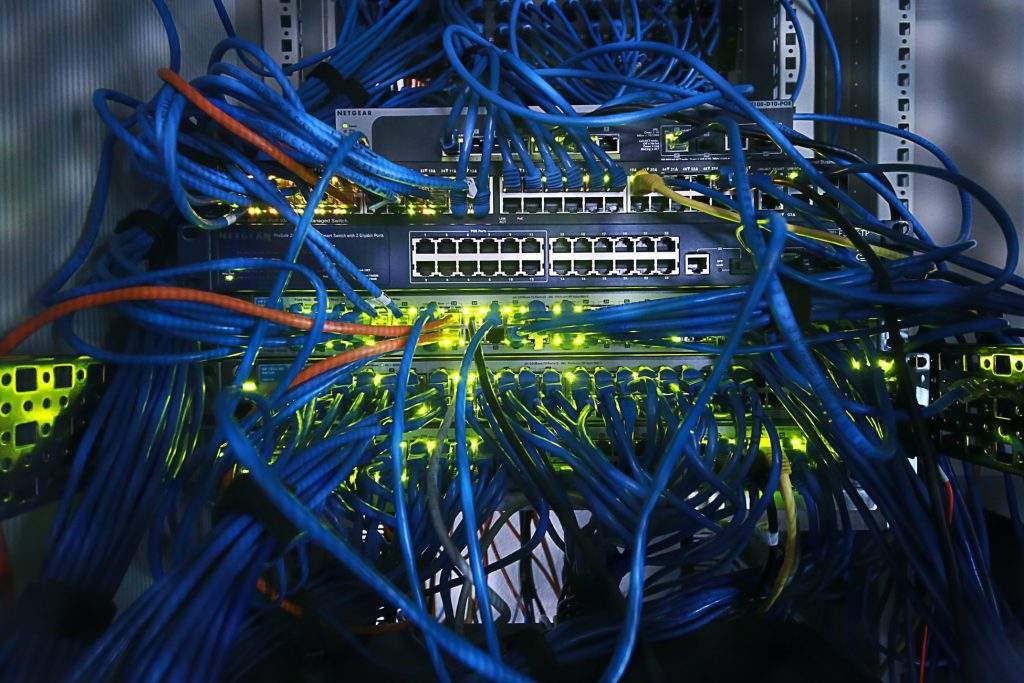
Telecommunication uses packets. No need to add “all” or “every” or even articles – the story goes so far back in time that it is no longer seen as “the invention” but rather as the conveniently adopted rule. The solution itself, however, is a Cold War brainchild fathered by (or at least strongly attributed to) Polish-American Paul Baran. That genius brought up more than one brilliant idea, but now we care for this one: a decentralized network that crushes a message into tiny parts, sends each of them its own way and at final destination light-fast reassembles an item to its normal shape. The reason for those, kinda, dispersed ways was to withstand the strike of the Soviets – not less!
Ok, back from history to data transfer. Network packets are really small: the tiniest could be only 64 bytes; the biggest chunks are about 1.5 Kb. An average text-only e-mail (no pix or other attachments) is 4 packets or like. Pony size does help a packet to get thru pretty much any needle’s eye, be it a router, a gateway, etc. The downside is here, too: the virtual Universe is full of stuff that senders would love to be delivered, while the receivers would hate getting. Deep Packet Inspection becomes a must in an array of Internet security issues of today.
Another brick in the wall
Network packets are often compared to usual, “snail mail” envelopes. Their structures are similar indeed: the header is (roughly) an addressee, the body contains what a normal letter or postcard should say, the footer is, roughly again, a sender.
Firewalls, those always-on-duty security watchtowers, are great in “in face” protection. They scan packets’ headers only: an openly hostile message will not be let thru, while something disguised as “recognizable”, with an unwanted content hidden deeper, can pass a firewall and cause harm.
Deep Packet Inspection (DPI) is called to deal with that deep. It checks both the addresses and body text and can even name a service or an application that generated this very packet. Most importantly: DPI user inputs verification parameters all by him/herself, analysis criteria are fully customizable. As easy as applying a filter to your mailbox, right? But DPI can go even further – for example, checking the ports against their habitual use or specifically created list. There are confirmed cases of network owners discovering, with the help of DPI, some serious abuse of their own networks – like creating peer-to-peer exchange of pirated films, for just one example…
Alas, DPI methods can also be used as an obstacle for the free flow of information. Later on this matter.
Flick of the switch
Another task DPI is equally good at is traffic organization. According to the criteria set, again, by a particular user, any packet can be detected, then not only blocked but also categorized and/or redirected in real time. This is critical for entities that care for both security and quality of their traffic, telecom operators and Internet providers to be named first.
Examples include (but are way too far from being limited to):
- A business that is focusing on sales – say, thru its own online store – yet demonstrates certain level of activity in social networks and video streams. DPI labels store-related traffic the foreground one while YouTube, Facebook, etc. are the 2nd rate from now on;
- A telecom provider – getting the clearest picture of “what my subscribers are”, including traffic use patterns, level of demand for any available service and scalable breakdowns of network peak loads. This goes for the mentioned “quality of traffic”, or, more savvy, for the best possible use of allocated bandwidths (QoS);
- Virtually any major (read – city or district) level utilities provider or emergency service. Information DPI recognizes as urgent can bypass any queues of ordinary data and be sent immediately. The same system can prevent 5G-related attacks by blocking malicious requests from devices in IoT framework;
- Any entity working predominantly with confidential or copyrighted information: think law enforcement, record label or publishing house. Packets non-compliant with DPI settings will not be let thru, thus preventing leaks of any unauthorized data. While fully compliant messages can go with no special permission for every send-out: rules are set in/by a DPI system.
Few shades of dark

DPI was unthinkable not too long ago due to simple matters. Everything was comparatively limited. Humble computing resources were making firewalls the ultimate solutions: they munch very little of processing power. Slim bandwidths were not intended for ample data flow, yet less capable of deep packet analysis.
DPI approach, as we already learned, emerged as a security tool, but can do much more and keeps developing. And the “must have” word combination was cited too. So, is Deep Packet Inspection truly the force being with you against the dark side?
Depends. Not on a system per se: human factor comes into play, as usual. Definitely on the dark side is the possibility to use DPI for censorship and spying. The government of China has managed to create its very own Great (Fire)Wall using DPI features. The outcomes, from one side, are very feasible: China has its own Facebook (WeChat), and dozens of other local services that substitute the global ones. On the other side it is plain frightening: DPI can cut a country as big as China from the World (Wide Web).
The most recent occurrence is the Internet blackouts in Belarus. Authorities, frequently referred to as “the last dictatorship of Europe”, were repeatedly curtailing the country’s (state owned) external gateway in order to deprive the protest movement of communication. As per official Minsk, the West was to blame, as if “blocking the access”. Pretty quickly it turned out that the certain, formerly Canadian, company was shipping the appropriate ware to Belarus. So in reality neither the entire traffic was halted, nor was the gateway shut down. Requests – all of them – were simply redirected to DPI. Causing an enormous traffic slowdown, almost the state-wide collapse.
Latest news: that formerly Canadian, name-starts-with-an-S company refused any further support for its Belarusian clients.
The above brings another not-so-bright issue. If you, accidentally or on purpose, routed all your traffic to DPI – experience The Slow. One more burden is the separate need for updates and revisions of DPI policies, since the method makes your protection more effective but somewhat complicated. So at least the initial launch requires highly skilled personnel.
Inspected. Recommended
Success stories where DPI implementation shifted, sometimes greatly refurbished businesses, are multiple.
Thinking strategically, DPI methods appear valuable solution to settle the issues of security, data protection/confidentiality, performance management (with applied network analysis), and some others.
Pure technical approach shows versatility of a method, together with its easiness to pair with the range of hardware and matchless detection potential, as the definite advantages of DPI.
Simply “thinking clients” means better traffic control and distribution – which, in turn, allows an operator to provide higher quality services to its customers.

 Previous article
Previous article